At DataTree Technology, we understand the critical importance of securing sensitive information in today’s digital landscape. Our Cybersecurity Maturity Model Certification (CMMC) services are designed to help your organization meet the rigorous standards required for Department of Defense (DoD) contracts. Whether you're a small business or a prime contractor, we simplify the process of achieving compliance by providing expert guidance and tailored solutions. Protecting your data is not just about meeting requirements—it’s about safeguarding the trust of your clients and partners.
Cybersecurity Maturity Model Certification (CMMC)

Comprehensive CMMC Gap Analysis
Achieving CMMC compliance starts with understanding where your organization stands. Our team conducts a thorough gap analysis to evaluate your current cybersecurity practices against the requirements of your desired CMMC level. We identify vulnerabilities, assess risks, and provide a detailed roadmap to help you achieve compliance efficiently. With DataTree Technology, you’ll have a clear understanding of the steps needed to secure your systems and protect sensitive information.

Tailored Implementation and Support
CMMC compliance is not a one-size-fits-all solution, and we pride ourselves on providing customized support for every client. Our experts work closely with your team to implement the necessary controls and processes, ensuring a seamless transition to compliance. From technical upgrades and policy creation to staff training, we guide you through every stage of the certification process. With DataTree Technology as your partner, you can focus on your business while we handle the complexities of compliance.
CYBERSECURITY MATURITY MODEL CERTIFICATION (CMMC) PROGRAM
What is CMMC?
The CMMC Program aligns with the Department of Defense’s (DOD) existing information security requirements for the Defense Industrial Base (DIB). It is designed to enforce the protection of sensitive unclassified information shared by the DOD with its contractors and subcontractors. The Program provides the DOD with increased assurance that contractors and subcontractors are meeting the cybersecurity requirements for non-federal systems processing Controlled Unclassified Information (CUI).
Key features of the CMMC Program:
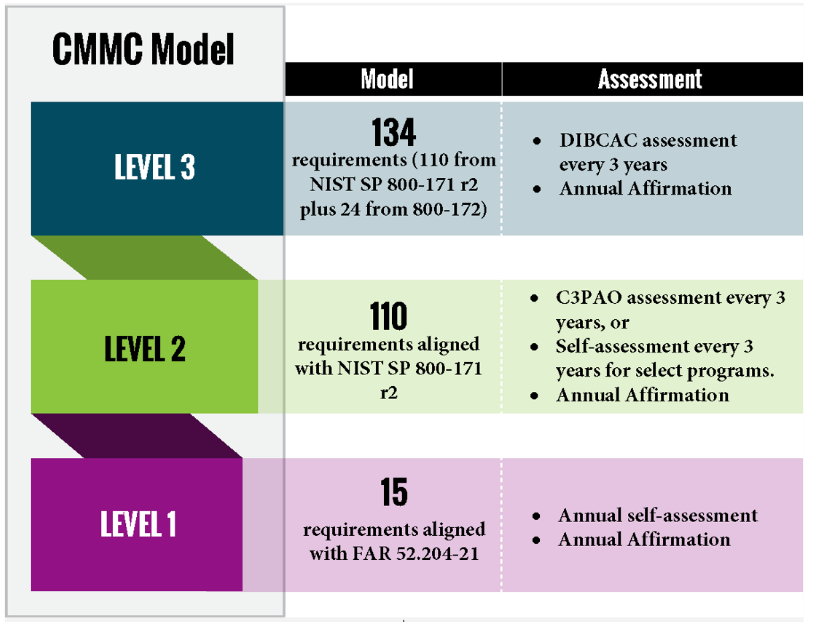
- Tiered Model: CMMC requires companies entrusted with sensitive unclassified DOD information to implement cybersecurity standards at progressively advanced levels, depending on the type and sensitivity of the information. The Program also outlines the process for requiring protection of information flowed down to subcontractors.
- Assessment Requirement: CMMC assessments allow the DOD to verify DIB implementation of existing cybersecurity standards.
- Implementation through Contracts: DOD contractors and subcontractors handling sensitive unclassified DOD information must achieve a specific CMMC level as a condition of contract award.
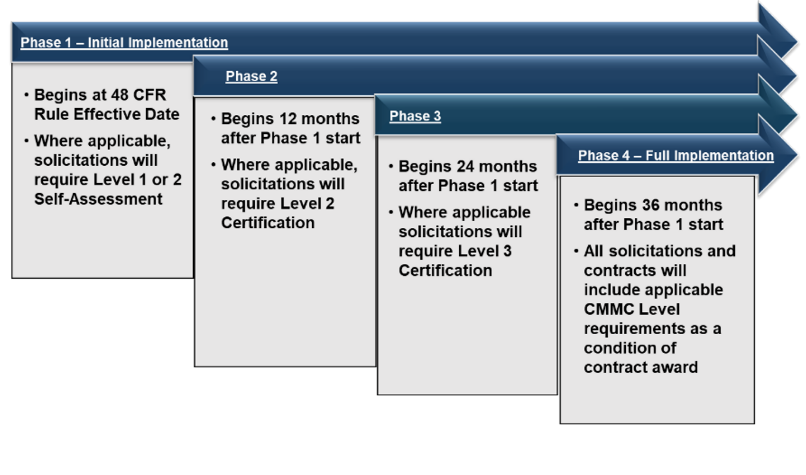
Proposed CMMC Program implementation timeline.
The CMMC Program implementation date is 60 days after the publication of the final Title 48 CFR CMMC acquisition rule. The Draft Title 48 CFR CMMC rule has been published, and the final rule is pending. CMMC assessment requirements will be implemented using a four-phase plan over three years. The phases add CMMC Level requirements incrementally, starting with self-assessments in Phase 1 and ending with full implementation of Program requirements in Phase 4.
If your organization has CUI and is pursing CMMC Level 2, do you still need a third-party assessment from a CMMC Third-Party Assessment Organization (C3PAO)?
- It depends. CMMC Level 2 will be split into two paths:
- Contracts that require an assessment from a C3PAO (every 3 years);
- Contracts where an annual self-assessment and affirmation from company leadership will suffice.
How will your organization know if CMMC applies to your DOD contract(s)?
- The DOD will specify the required CMMC level in the solicitation and in Requests for Information (RFIs), if utilized.
Do prime contractors and subcontractors need to be at the same level?
- If contractors and subcontractors are handling the same type of FCI and CUI, then the same CMMC level will apply. In cases where the prime contractor only flows down select information, a lower CMMC level may apply to the subcontractor.
Other key items your organization should be aware of?
- Under Defense Federal Acquisition Regulation Supplement (DFARS) 252.204-7012, contractors were expected to have implemented all 110 controls in National Institute of Standards and Technology (NIST) Special Publication (SP) 800-171 no later than December 31, 2017.
- NIST SP 800-171 and CMMC Level 2 translate to 320 Assessment Objectives (AOs) defense contractors need to meet.
- The False Claims Act (FCA) is still a very real enforcement mechanism, and the Department of Justice (DOJ) has already been taking a stronger stance regarding cyber violations.
How are we well-positioned to help your organization prepare for CMMC?
- We have a dedicated team of cybersecurity experts, including a Lead CMMC Certified Assessor (Lead CCA), and CMMC Certified Professionals (CCPs) who have prepared clients for CMMC Self-assessments and C3PAO assessments.
- We have advised “how-to” build and maintain numerous CMMC Level 1 and Level 2 compliant Information Systems.
Specifically, what CMMC services can we provide your organization?
- Identification of the needed CMMC level, based on current DOD work, and existing contract clauses.
- Risk mitigation strategies to more effectively manage and reduce cybersecurity risk.
- Full Cybersecurity Programs including, but not limited to, System Security Plans (SSPs), Cybersecurity Policies and Procedures, Shared Responsibilities Matrices (SRMs), Implementation Schedules, Self-Assessment advising, and Plans of Action & Milestones (POAMs).
- Assistance with enrolling and uploading your self-assessment score in the Supplier Performance Risk System (SPRS).
- Continued education and training as DOD cybersecurity rules and standards evolve.
- Prepare for CMMC with confidence.
- DataTree Technology is assisting DOD suppliers throughout the U.S. navigate the complexities of CMMC. With DataTree Technology, you can achieve a high-quality evaluation of your current cybersecurity posture and learn how best to obtain your desired CMMC level. To gain a competitive advantage, consider successfully completing your CMMC compliance now.